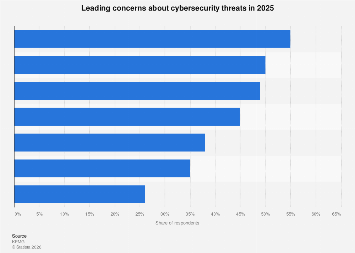
As the digital frontier continues to expand, so too do the sophisticated and multifaceted threats that jeopardize businesses, governments, and individuals alike. Looking ahead to 2025, the cybersecurity landscape is poised for further evolution, driven by advancements in artificial intelligence, the proliferation of the Internet of Things (IoT), and the persistent ingenuity of malicious actors. Understanding these emerging concerns is no longer a reactive measure but a proactive imperative for ensuring resilience in an increasingly interconnected world.
One of the most significant shifts anticipated is the increasing sophistication of AI-powered cyberattacks. While AI has become a powerful tool for defense, its offensive applications are equally potent. Malicious actors are leveraging machine learning algorithms to automate the discovery of vulnerabilities, craft highly personalized phishing campaigns that are exceptionally difficult to detect, and develop adaptive malware that can evade traditional signature-based detection methods. This arms race between AI for offense and AI for defense means that security solutions must continuously evolve to stay ahead. For instance, AI can be used to generate deepfake audio and video for social engineering attacks, making it harder to distinguish between legitimate communications and deceptive ones. The financial implications of such sophisticated attacks are substantial, with estimates from various cybersecurity firms suggesting that the global cost of cybercrime could exceed $10.5 trillion annually by 2025.
The burgeoning Internet of Things (IoT) ecosystem presents a vast and often vulnerable attack surface. With billions of connected devices in homes, industries, and critical infrastructure, each device represents a potential entry point for cybercriminals. Many IoT devices are designed with cost and convenience as primary considerations, often neglecting robust security measures. This creates a fertile ground for botnets, distributed denial-of-service (DDoS) attacks, and data breaches. The sheer scale of interconnected devices means that a single compromised IoT device could potentially lead to a cascade of security failures across an entire network or even disrupt essential services. The challenge lies in securing these diverse and often resource-constrained devices, requiring innovative approaches to authentication, encryption, and regular patching across a heterogeneous environment. Industry analysts predict that the number of connected IoT devices will surpass 29 billion by 2025, underscoring the urgency of addressing IoT security.
Ransomware continues to be a formidable threat, evolving from encrypting individual files to more insidious forms of extortion. "Double extortion" tactics, where attackers not only encrypt data but also steal it and threaten to release it publicly if the ransom is not paid, have become commonplace. Furthermore, "triple extortion" is emerging, involving the threat of launching DDoS attacks or contacting customers and partners of the victim organization. The financial impact of ransomware attacks is staggering, with average ransom demands escalating and the cost of recovery, including downtime and remediation, often far exceeding the ransom itself. The global cost of ransomware attacks is projected to reach $265 billion per year by 2031, according to Cybersecurity Ventures, a trend that will undoubtedly continue to impact businesses significantly in 2025. Organizations are increasingly adopting proactive measures, such as robust data backup strategies and comprehensive incident response plans, to mitigate the damage.
Supply chain attacks represent another critical area of concern. By compromising a trusted third-party vendor or software provider, attackers can gain access to the networks of numerous downstream organizations. The SolarWinds attack in late 2020 served as a stark reminder of the pervasive impact of such breaches, affecting government agencies and private companies worldwide. The complexity of modern global supply chains, with their intricate dependencies on various software and hardware components, makes them inherently difficult to secure comprehensively. Identifying and mitigating risks throughout the entire supply chain requires a collaborative effort between organizations and their partners, focusing on vendor risk management, code integrity, and continuous monitoring. The potential for widespread disruption makes supply chain attacks a strategic threat to national security and economic stability.
The increasing reliance on cloud computing, while offering immense benefits in terms of scalability and flexibility, also introduces new security challenges. Misconfigurations in cloud environments are a leading cause of data breaches, as organizations may inadvertently expose sensitive information by failing to implement proper access controls and security settings. The shared responsibility model of cloud security, where both the cloud provider and the customer have security obligations, can sometimes lead to confusion and gaps in protection. As more critical business functions migrate to the cloud, securing these environments effectively, including multi-cloud and hybrid cloud setups, will be paramount. The global cloud computing market is expected to continue its rapid growth, highlighting the ongoing need for specialized cloud security expertise and robust security frameworks.
The human element remains a persistent vulnerability. Social engineering tactics, including phishing, spear-phishing, and pretexting, continue to be highly effective because they exploit human psychology rather than purely technical flaws. As cybercriminals become more adept at crafting convincing lures, employee training and awareness programs are crucial. However, the effectiveness of these programs can be enhanced by incorporating more sophisticated simulation exercises and adopting a culture of security consciousness throughout an organization. The increasing use of remote workforces further complicates security efforts, as employees access company resources from diverse and potentially less secure networks. Implementing strong multi-factor authentication and endpoint security solutions becomes even more critical in such distributed environments.
Geopolitical tensions also play an increasingly significant role in the cybersecurity landscape. State-sponsored cyberattacks are becoming more frequent and sophisticated, often targeting critical infrastructure, intellectual property, and electoral processes. These attacks can have far-reaching consequences, impacting national security, economic stability, and public trust. The attribution of such attacks can be challenging, leading to complex diplomatic and retaliatory responses. International cooperation and the development of clear norms of behavior in cyberspace are essential for mitigating these risks, though progress in these areas remains slow. The potential for cyber warfare to escalate conflicts is a growing concern for global policymakers.
Finally, the increasing volume and complexity of cyber threats necessitate a shift towards more proactive and intelligent security strategies. This includes embracing security automation, leveraging threat intelligence feeds, and adopting a zero-trust security model, which assumes that no user or device can be implicitly trusted, regardless of their location. Continuous monitoring, anomaly detection, and rapid incident response capabilities are no longer optional but essential components of a robust cybersecurity posture. Organizations that prioritize a holistic and adaptive approach to security, integrating technology, processes, and people, will be best positioned to navigate the evolving threat landscape of 2025 and beyond. The economic imperative for strong cybersecurity is undeniable, with businesses that fail to adapt facing not only financial losses but also significant reputational damage and potential regulatory penalties.