The rapid globalization of the remote workforce, accelerated by the post-pandemic digital shift, has inadvertently birthed a sophisticated new frontier for geopolitical espionage and illicit financing. Across the European Union and the United Kingdom, corporate boardrooms and cybersecurity departments are grappling with a burgeoning crisis: the infiltration of their payrolls by highly skilled IT professionals who are not who they claim to be. These "fake workers," directed by the Democratic People’s Republic of Korea (DPRK), are increasingly utilizing generative artificial intelligence to bypass traditional vetting processes, effectively turning the European tech sector into a silent funding engine for Pyongyang’s prohibited weapons programs.
For years, the phenomenon of North Korean IT workers masquerading as Western freelancers was largely viewed as a North American problem. However, recent intelligence reports and corporate security audits indicate a strategic pivot toward European markets. This shift is driven by Europe’s high demand for specialized software developers and a perceived regulatory landscape that, while robust, is currently struggling to keep pace with the hyper-realistic deceptions enabled by modern AI tools. The scale of the operation is vast, with thousands of state-sponsored operatives living primarily in China and Russia, yet presenting themselves as local residents of cities like Berlin, London, or Paris.
The mechanism of this deception is as ingenious as it is alarming. At the heart of the scheme is the use of generative AI to create synthetic identities. In the past, fraudulent candidates might have relied on stolen social security numbers and poorly photoshopped identification. Today, they utilize AI-driven image generation to create professional-grade LinkedIn profiles and deepfake technology to conduct live video interviews. By layering real-time voice modification software over their own, these operatives can mask North Korean accents, adopting regional European inflections or perfect "international English" that disarms unsuspecting HR managers.
Beyond the initial hire, the operational infrastructure required to maintain this ruse is complex. Central to the strategy is the "laptop farm." To avoid triggering geographic security alerts, North Korean operatives contract with "mules" located within Europe. These intermediaries receive corporate laptops and set them up in residential apartments, connecting them to local Wi-Fi networks. The North Korean worker then accesses the laptop via remote desktop software from a different continent. To the company’s internal IT monitoring systems, it appears as though a dedicated employee is working diligently from a suburban flat in Munich or a co-working space in London, when in reality, the code is being written from a government-controlled facility in Vladivostok or Dandong.
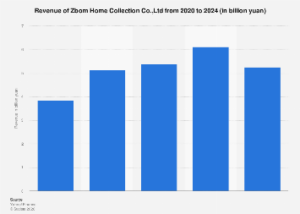
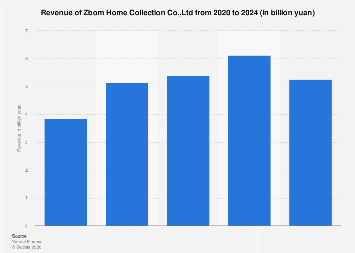
The economic implications of this infiltration are staggering. The United Nations and the U.S. Department of Justice have estimated that these IT workers can generate hundreds of millions of dollars annually for the Kim Jong Un regime. Unlike traditional state-sponsored hacking, which relies on high-risk theft or ransomware, the IT worker scheme provides a steady, legitimate-looking stream of hard currency. These individuals often hold multiple full-time positions simultaneously, earning high-six-figure salaries in Euros or Pounds. Intelligence analysts suggest that as much as 90% of these earnings are siphoned back to the North Korean state, directly circumventing international sanctions intended to cripple the country’s nuclear and ballistic missile capabilities.
However, the threat extends far beyond the financial drain. While many of these workers appear to be "model employees"—delivering high-quality code and meeting deadlines to ensure their continued employment—the security risks are existential. By gaining administrative access to corporate repositories, cloud infrastructure, and proprietary databases, these operatives effectively serve as "sleeper cells." There have been documented instances where North Korean IT workers, upon being terminated or fearing discovery, have transitioned into malicious actors. They have been known to install backdoors for future state-sponsored cyberattacks, exfiltrate sensitive intellectual property, or attempt to extort their former employers by threatening to leak confidential data.
European tech firms are particularly vulnerable due to the prevailing "talent war" in the software engineering sector. According to recent industry data, the EU faces a shortage of over 500,000 ICT professionals. In this high-pressure environment, HR departments are often incentivized to shorten the "time-to-hire," sometimes cutting corners on background checks or relying on third-party recruitment agencies that may not have the sophisticated forensic tools required to spot AI-generated fraud. Furthermore, the cultural emphasis on trust and the proliferation of fully remote "nomad" work styles have made the rigorous physical verification of employees seem like an outdated relic of the pre-digital age.
The response from the European regulatory and law enforcement community is beginning to coalesce, albeit slowly. The European Union Agency for Cybersecurity (ENISA) has recently updated its threat landscape reports to highlight the rise of synthetic identities in corporate espionage. National security agencies across the continent are issuing classified briefings to major financial institutions and defense contractors, warning of the specific hallmarks of North Korean infiltration. These include requests to be paid in cryptocurrency, a refusal to appear on camera for spontaneous meetings, and inconsistencies in time-zone availability.
Market data suggests that the cost of defending against this threat is rising. Corporations are now being forced to invest in "Identity Proofing" solutions that use biometric liveness checks—requiring a candidate to perform specific physical movements during a video call to prove they are not a deepfake. Additionally, there is a growing market for specialized cybersecurity firms that conduct "digital footprint audits," verifying that a candidate’s online history is consistent with their claimed experience and not a curated AI fabrication.
From a global perspective, the North Korean IT worker program represents a masterclass in asymmetric warfare. By exploiting the very tools that Western economies have built—globalized remote work, AI, and decentralized finance—Pyongyang has found a way to remain economically viable despite being the most sanctioned nation on earth. This creates a complex ethical and operational dilemma for European companies. A firm that unwittingly hires a North Korean operative is not just a victim of fraud; it is, in the eyes of international regulators, a party to the financing of a prohibited weapons program, potentially facing massive fines and reputational ruin.
As we look toward the future, the arms race between AI-enabled deception and AI-enabled detection will only intensify. The emergence of more sophisticated Large Language Models (LLMs) means that North Korean operatives can now write flawless documentation, emails, and code comments in any European language, removing the linguistic "tells" that previously helped security teams identify them. The "fake worker" phenomenon is no longer a peripheral nuisance; it is a central challenge of the modern digital economy.
To mitigate this risk, European business leaders must move beyond a purely technical response. A holistic approach is required, one that combines rigorous biometric verification with a culture of security awareness that extends into the HR department. Verification of physical address, in-person onboarding where feasible, and the use of hardware-based multi-factor authentication (MFA) that cannot be easily shared across borders are becoming the new baseline for corporate security. In an era where the person on the other side of the screen might be a digital ghost working for a rogue state, the old adage of "trust but verify" has never been more critical to the survival of the enterprise.